In this day and age, cybersecurity needs to be taken very seriously. Over the last few years, we’ve seen an increase in both cyber-attacks and new regulations and methods that need to be implemented to combat them. Still, in most locations, you can do a gb whatsapp apk download without raising any red flags.
Most of these attacks and/or breaches have been centered around getting personal data that can then be used for something as benign as targeted marketing campaigns or something much more nefarious such as selling your data on the black market.
In the worst case scenario, this can lead to identity theft, with hackers abusing your data for their own financial gain or even criminal purposes. Protecting yourself from these threats saves you from having to face astronomical credit card bills or even warrants for your arrest.
Naturally, while personal data collection is the most prominent threat, it’s in no way the only one. DDoS attacks will look to overload your site with bogus traffic, therefore disabling real users’ access to your content. Relatively older but still in use are also various types of keyloggers, viruses, and trojans. All of them are based around software that’s, in one way or another, installed on your computer. This software will either record all data you enter through the keyboard and mouse, replicate indefinitely until your computer becomes inoperable, or allow hackers direct access to your data that can then be copied, modified, or deleted.
Everything that revolves around cybersecurity is intrinsically linked. As hackers develop new ways to get to data they shouldn’t, security experts are developing new ways to stop them. It’s a never-ending cycle with both sides of the coin trying to get the upper hand but never succeeding, at least not in the long term.
Since we’re on the side of the good guys, we’ve gone through some of the best ways to protect both your data and that of your users.
1. Use VPNs

You’ve probably seen ads around the web that warn you about the dangers of browsing without the protection of a VPN. Usually, you’d just glance over them and go on with what you’re doing, but those warnings aren’t as benign as you think.
First of all, let’s cover what VPNs are.
A VPN, or virtual private network, without getting too technical, masks your IP address, creating a private network connection from a public connection, thereby ensuring anonymity and privacy. This switch safely eliminates many of the aforementioned dangers you could face from malicious software.
One big problem with VPNs is that there are many solutions that provide the service, so it’s really hard to figure out which is the best for you; keep in mind that there isn’t a universal solution, but instead, you’ll most likely fare better if you target a service focusing on something specific that you’re also looking for.
Luckily, there’s a website that brings all relevant VPN providers into one place, sorting and ranking them to hand you enough data to make an informed decision – VPNSurfers.
To put it bluntly, VPNSurfers is a list redirecting you to services; however, it’s much more than that. You’ll get access to reviews, comparisons, and services that are even sorted by niche for easier navigation. Snippet reviews are offered for every service featured on the site, with the addition of more in-depth reviews for popular services.
If you don’t want to bother with reading reviews and prefer a more ratings-oriented overall system, don’t worry because everything is rated in a familiar five-star manner.
On the other hand, the in-depth reviews go really deep, and they’re all structured the same way (similar to a FAQ section), hitting all the same points before arriving at the ultimate conclusion. This concept makes it really easy to compare all the key features yourself, but even that isn’t necessary if you don’t want to skip back and forth between tabs/windows because you’ll find premade comparisons ready and waiting.
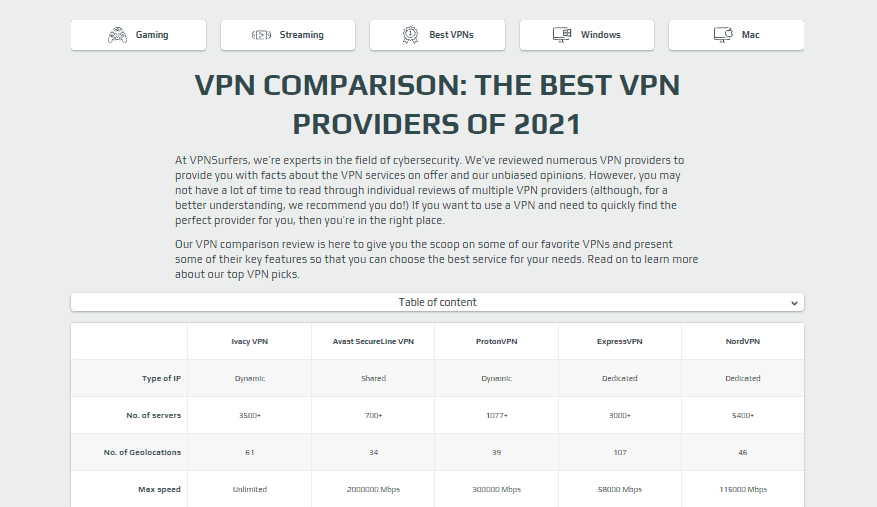
Comparisons offer a detailed table upfront for quick and easy access to data you’re most likely looking for while at the same time, again, providing more in-depth analysis for those that are hungry for that extra bit of data.
Finally, all the services are conveniently sorted into sections. Just to name a few, these sections include best budget VPNs, best corporate VPN solutions, best new VPNs, best VPNs for gaming, and more. Since the database is substantial, having predetermined filters can save you the time you can then spend researching services within the designated section, not wasting your time on a whole batch.
To show how complimentary VPNs are to other services in the field of cybersecurity, there’s the antivirus section; more precisely, a section explaining how well various antivirus software interacts with your VPN of choice. Once again, the section is divided into two parts – the first shows how well a VPN works with antivirus software, while the second gives you a preview into some of the most popular antivirus services.
2. Avoid public Wi-Fi

Since it is closely connected to VPNs, we need to talk about public Wi-Fi. The first thing most of us do when we come to a new location is asking for the Wi-Fi password without thinking too much about it. That isn’t the best idea. Don’t let the presence of a password fool you. Although password-protected, public Wi-Fi is usually the perfect spot for malicious attacks – anyone can connect to the same network, and it’s hard to pinpoint from where the attack came.
Because using Wi-Fi is still the better method to connect to the web than any data plan you might have, it’s very hard to recommend not using public Wi-Fi at all – that’s just not realistic. Instead, we go back to the already mentioned VPNs.
Since they essentially turn public connections into private ones (or at least provide the illusion of doing so), VPNs are the perfect tool to combat the most common threats associated with public Wi-Fi.
3. Use strong passwords and two-factor authentication
We’ll all admit that it’s more than tedious to be registering on a new site since the password requires you to use small and big letters, numbers, symbols, hieroglyphics, Latin proverbs, and the long-forgotten language of the Mayans – with no spaces. Over time password requirements have become more and more elaborate. However, these requirements are put in place for the sole reason of protecting your data (both private and personal). It’s recommended that you use random passwords or even full phrases and change them at least every three months to ensure the best results. Also, try not to use the same password on every service and every device you have – yes, it’s easier, but it can lead you to trouble down the line.
A step above a singular password (no matter how complex) is two-factor authentication.
Before, when smartphones were seen only on SF shows, tokens were used for two-factor authentication, almost exclusively by banks. Now, with access to the hardware and affordable internet virtually everywhere, two-factor authentication is easily implemented through various apps we use daily.
4. Keep your (antivirus) software up to date

This one is essentially a no-brainer. As we’ve already mentioned, hackers and security experts are in a vicious cycle trying to outdo one another. Every time some new malicious software pops up, not long after, so does a patch that guards against it.
Suppose you aren’t regularly updating your antivirus software and your software in general, for that matter. In that case, you’ll be falling behind in that cycle and therefore leaving the door wide open for intrusions. Luckily, most software nowadays, from operating systems on all devices to antivirus apps and everything in between, has automated updates. With this feature turned on, you won’t have to keep track of all the newly released updates; at most, you’ll be required to authorize an installation, but more often than not, the process is done in the background without you even knowing it.
5. Use firewalls
Very similar to antivirus software, firewalls work great as the first line of defense against anything that could potentially be thrown at you. In some cases, you’ll be notified that harmful software is trying to access your data, and in other cases, that software will be outright blocked.
Default firewalls come from several places – both Windows and macOS have an integrated firewall on which you can change the settings for more or less protection. Additionally, your router should also have a firewall built in to protect the network at the source.
The bad aspect of firewalls is the effect they have on performance. Because they screen everything that comes their way, you’ll sometimes experience more strain put on your computer, making everything slower than it would be without a firewall. Still, somehow, that’s a small price to pay for the added security.
As you would expect, the stronger your hardware and internet connection, the less you’ll feel everything slowing down.
6. Backup your data

You should always backup your work. There probably isn’t one person among us that hasn’t been told that at least once. Unfortunately for us, it’s hard to learn from someone else’s mistakes, and usually, we have to lose some data before we wise up.
Backups should be made both on the cloud, for easy access anywhere you are, and on physical drives not connected to the web for extra security. Having backups in place will not directly protect you from a potential attack but will make coping with it much easier. Even if you ultimately have to break everything down and start anew, it will be that much simpler and quicker because of the data you’ve backed up.
You could set up automatic backups that transfer your data to the cloud, or you could transfer the data manually onto an external hard drive, for example – there are many ways of going about the backup process, but one thing can’t be denied; it’s one of the crucial steps you can take in order to improve your cybersecurity.
7. Follow up on current news in cybersecurity

This last measure is also the one with the broadest reach. You won’t know what software is best to use if you don’t know what the threats are. Of course, nobody expects you to suddenly become a certified expert by reading an article or two, but in order to ensure your protection, you’ll need to read up on these topics and do so from the perspective of both sides.
The first thing would be to know the threats that are circulating the web at a given moment. The second is to know what software has been developed in response to these threats and implement it accordingly.
Some of these methods don’t require any direct action on your part. On the other hand, others give more access to a hacker but require some type of action from you. Something along the lines of giving away your data in a phishing email and/or opening unsafe files. In those instances, the fallout could be drastic and far-reaching (leaving entire operating systems in a nonfunctional state in worst-case scenarios). So, knowing what the most commonly used threats at any given time are, is invaluable.
8. Have the best security plugins
WP Login Lockdown is a highly useful plugin for WordPress websites that helps prevent brute force attacks on the login page. This plugin limits the number of login attempts that can be made within a specific period and locks out users who exceed these limits. It also logs all failed login attempts, providing valuable information for site owners to analyze and address potential security threats. With the increasing number of cyber attacks, it is important to stay vigilant and take proactive measures to secure your website. By using WP Login Lockdown, website owners can add an extra layer of protection to their login page and prevent unauthorized access to their website.
WP Force SSL, on the other hand, is a security plugin that ensures all traffic to and from a website is encrypted using SSL. SSL is the most commonly used security protocol for websites, and it is recommended to use a security certificate whenever personal information needs to be transmitted between the website and the database or web server. This is especially important as cybercriminals are always looking for ways to capture sensitive information and use it to gain unauthorized access to a website or user accounts. By implementing WP Force SSL, website owners can ensure that their website traffic is encrypted, reducing the risk of interception or data theft by malicious actors.
In conclusion, both WP Login Lockdown and WP Force SSL are essential plugins for improving the overall cyber security of a WordPress website. WP Login Lockdown helps prevent unauthorized access to the login page, while WP Force SSL ensures that website traffic is encrypted, reducing the risk of data theft. By implementing these plugins, website owners can significantly improve the security of their website, protect their reputation, and safeguard their user’s data.
Summary
New attack methods are being devised every day, and sure, much of the protection you’ll need is automated nowadays, but there are still some actions you’ll have to take manually for full protection.
It’s important to stay ahead of the curve, so you don’t get blindsided and find your data lost, or even worse, stolen.
We’ve listed some of the simplest yet most effective ways to prevent anything like that from happening, and all of them are worth looking into, especially if it is something as painless as going through a list and picking the best option for yourself, as you’ll do with the VPNSurfers database.
Really Awesome Post. It is such a Master Piece you’ve created. Thanks buddy! I’ve read it completely. Thanks Again! Keep up the Good work.
This is the best kT. Thanks for the wonderful Knowledge Sharing. I am also writing one blog. Pls, give me an idea about writing well blog.. I am damn sure you will become the best content developer.